Set up your prerequisites from the first issue. This is Crux of The Matter.
Identification
We have two mutually independent executable samples to study; Lab01-02.exe and Lab01-03.exe. As usual, don’t sweat the file names, keep calm and upload to VirusTotal.
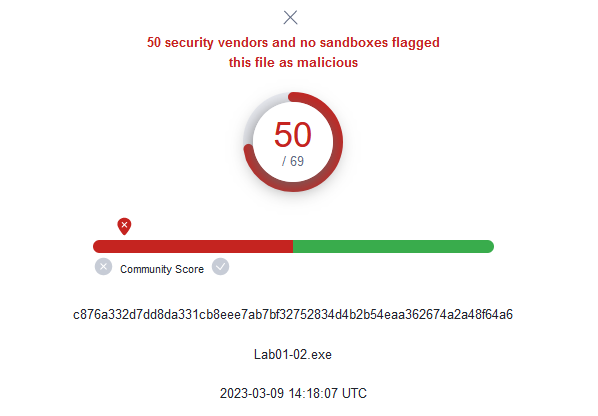
VirusTotal ‘summary’ tab on Lab01-02.exe;
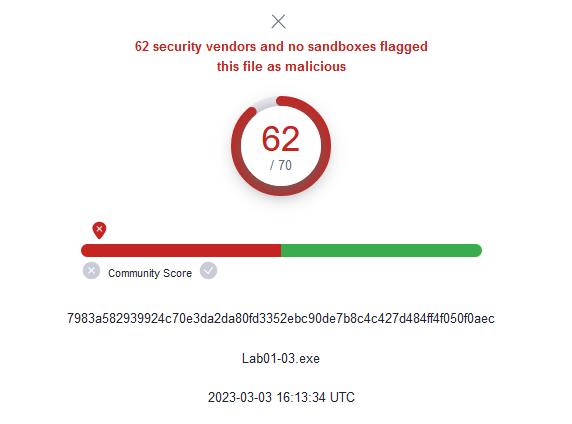
VirusTotal ‘summary’ tab on Lab01-03.exe;
With that, we have the hashes and antivirus detection information on both files. Next we navigate to the ‘details’ tab to inspect the executables’ code sections for signs of packing and obfuscation.
Lab01-03.exe suggests packing by some ‘FSG 1.0 → dulek/xt’ packer. However, having only the UPX packer at this time, we cannot analyse this file any further.
On the other hand, Lab01-02.exe has it’s sections interestingly named UPX0, UPX1 and UPX2. This is typical of UPX-packed malware and their sizes should be carefuly noted.
As shown, the raw size on the sections; UPX0, UPX1 and UPX2, are significantly smaller than their respective virtual sizes. The UPX0 section, for example, with a virtual size of 16384 bytes and a raw data size of 0 bytes sticks out rather sorely. Clearly, Lab01-02.exe is packed and to proceed with further analysis, we have to unpack it. Navigate to directory of your now downloaded UPX packer and run the following command:
upx -o outputfilename -d originalfilename
to produce output like below:
NOTE: ‘-d‘ option indicates a decompress action and the ‘-o‘ option specifies the filename for the decompressed execuatable.
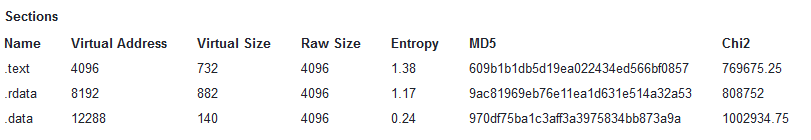
Uploading the now decompressed/unpacked Lab01-02.exe sample in VirusTotal we get a completely new look at the section information with regular sized code sections.
Characteristics and behaviour.
With the Lab01-02.exe sample now unpacked, we can properly check for the sample’s import information on VirusTotal:
ADVAPI32.dll (advanced API) is a part of the Windows advanced API services library. Think of it as an extension of KERNEL32.dll that provides additional advanced functionality like manipulating the Windows registry, restarting and shutting down the system, starting/stopping and creating Windows services, and managing user accounts.
Regarding WININET.dll, the Windows documentation describes the DLL as developed to “…assist you in making the Internet an integral part of any application. The new functions, contained in WININET.DLL, simplify accessing the Internet using HTTP (Hypertext Transfer Protocol), FTP (File Transfer Protocol), and gopher“.
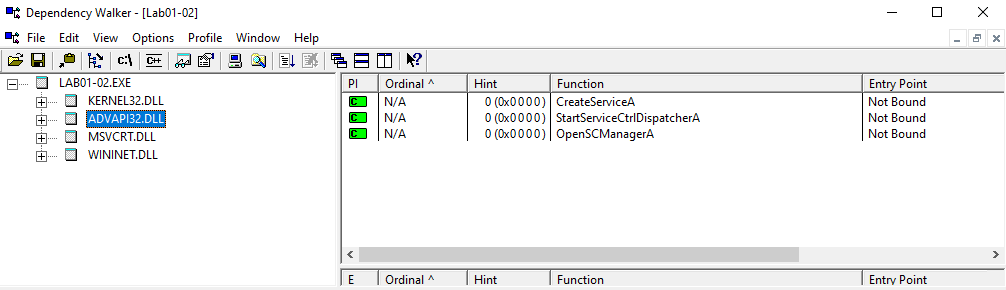
With that, we recover functions imported during execution by these DLLs by loading the Lab01-02.exe sample into Dependency Walker.
KERNEL32.dll exports: LoadLibraryA(), GetProcAddress(), VirtualProtect(), VirtualAlloc(), VirtualFree(), ExitProcess(), SystemTimeToFileTime(), GetModuleFileNameA(), CreateWaitableTimerA(), OpenMutexA(), SetWaitableTimer(), WaitForSingleObject(), CreateMutexA(), CreateThread().
ADVAPI32.dll exports: CreateServiceA(), StartServiceDispatcherA(), OpenSCManagerA().
WININET.dll exports: InternetOpenUrlA(), InternetOpenA().
The most interesting imports from these DLLs; CreateServiceA() from ADVAPI.dll and InternetOpenUrlA()/InternetOpenA() from WININET.dll suggest that the executable creates a service somewhere along it’s execution and makes internet connections to some URL we might find hardcoded as a string.
Host-based indicators and network-based indicators.
Running the Lab01-02.exe executable on Strings like so;
strings filename.exe
we recover a few strings as obvious flags to pay attention to:
A URL; ‘www.malwareanalysisbook.com’ and what might be a service; ‘MalService’. The InternetOpenURL() function imported by WININET.dll enables connections to the hard-coded URL, while the CreateService() function imported by ADVAPI32.dll creates the suspiciously looking ‘MalService’. We could take the presence of a ‘MalService‘ created at startup to be a host-based indicator and network traffic to the ‘www.malwareanalysisbook.com‘ URL to be a network-based indicator.
With that, we conclude our analysis. Further dynamic analysis could provide further insight on the dynamic behaviour of the Lab01-02.exe sample to confirm or refute the information recovered so far. Shout out to the Windows API docs and see you in a few days.